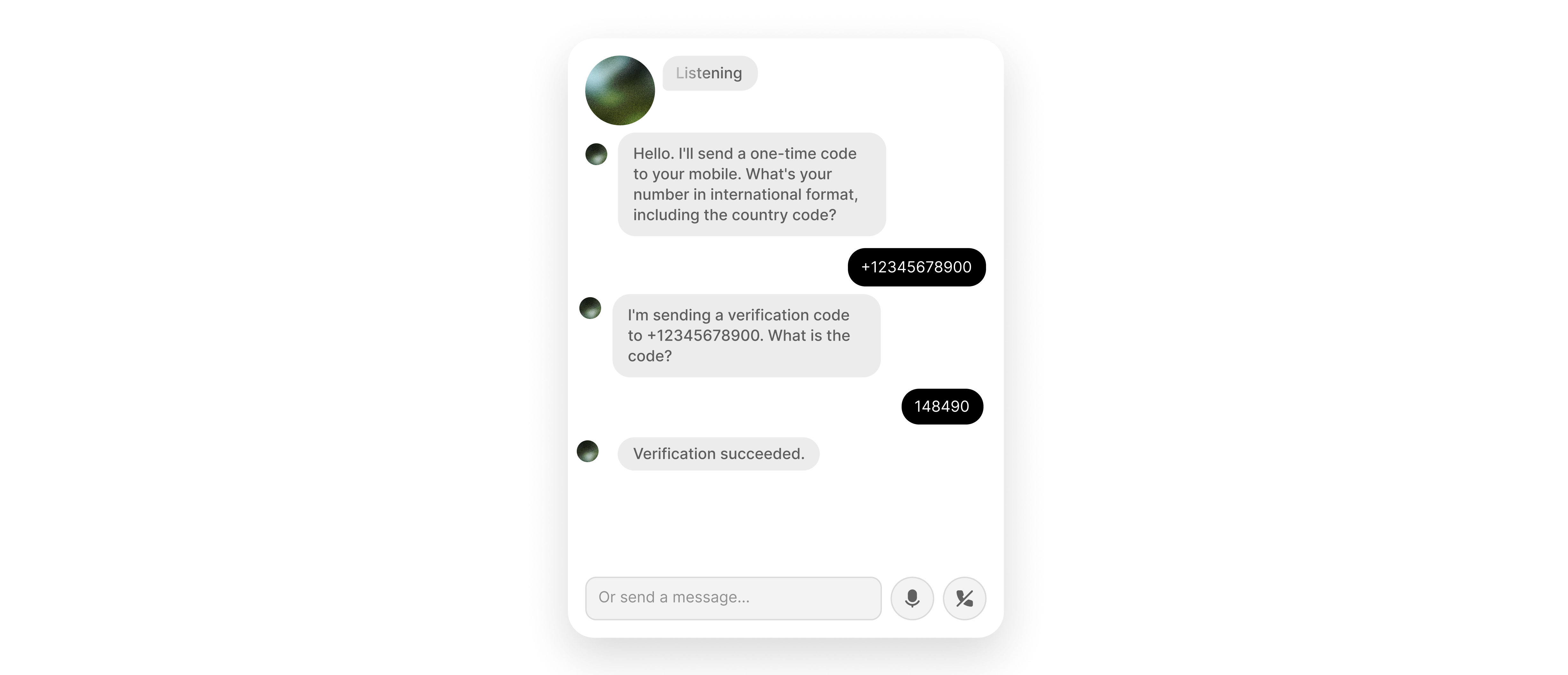
SMS OTP verification
Send and verify one-time passcodes over SMS during an agent conversation using Twilio Verify.
Overview
This guide shows you how to integrate Twilio Verify with your ElevenLabs agent so you can send an OTP to a caller’s phone number and verify the code they read back during a live voice conversation.
You will learn how to:
- Create a Twilio Verify service and Base64-encode your credentials for authentication.
- Configure two webhook server tools (
send_SMS_verificationandcheck_SMS_verification) in the dashboard, with the Agents CLI, or using the ElevenLabs API. - Authenticate both webhook calls using an
Authorizationheader with a secret value. - Enable the
skip_turnsystem tool so the agent waits when the caller has not received the code yet.
Prerequisites
- A Twilio account with Twilio Verify enabled. If Verify is not available in your Twilio Console, request access through Twilio support or your Twilio account team.
- If your Twilio account is in trial mode, the destination phone number must be a verified caller ID in Twilio.
Create an Authenticate (Verify) service
In the left sidebar, choose Add + and create an Authenticate (Verify) service.
Copy the Verify Service SID
Open the service Settings page and copy the Verify Service SID. It starts with VA and is different from your Account SID.
Common Mistake: Use your Verify Service SID (VA...) from the Authenticate (Verify) service in the tool URLs below. Do not put your Account SID (AC...) in the path. The Verify API expects the service SID in the URL; using the Account SID produces 4xx invalid-parameter errors.
You can use the Twilio API Explorer in the console to test requests before you attach them to your agent.
Encode credentials and configure webhook tools
Encode your Twilio credentials for Basic authentication
Twilio Verify uses HTTP Basic authentication with your Account SID as the username and Auth Token as the password. Find both under Account Info on the Twilio Console home page.
In your shell, Base64-encode ACCOUNT_SID:AUTH_TOKEN (colon-separated, no spaces):
Copy the output. The full Authorization header value is the word Basic, a single space, and that Base64 string. Store it as a tool secret in the next steps.
Configure the send_SMS_verification and check_SMS_verification tools
send_SMS_verification calls Twilio Verify to send an SMS OTP. check_SMS_verification submits the digits the caller speaks. Both require the same Verify Service SID and the same Authorization secret.
Add via the dashboard
Add via the CLI
Add via the API
send_SMS_verification
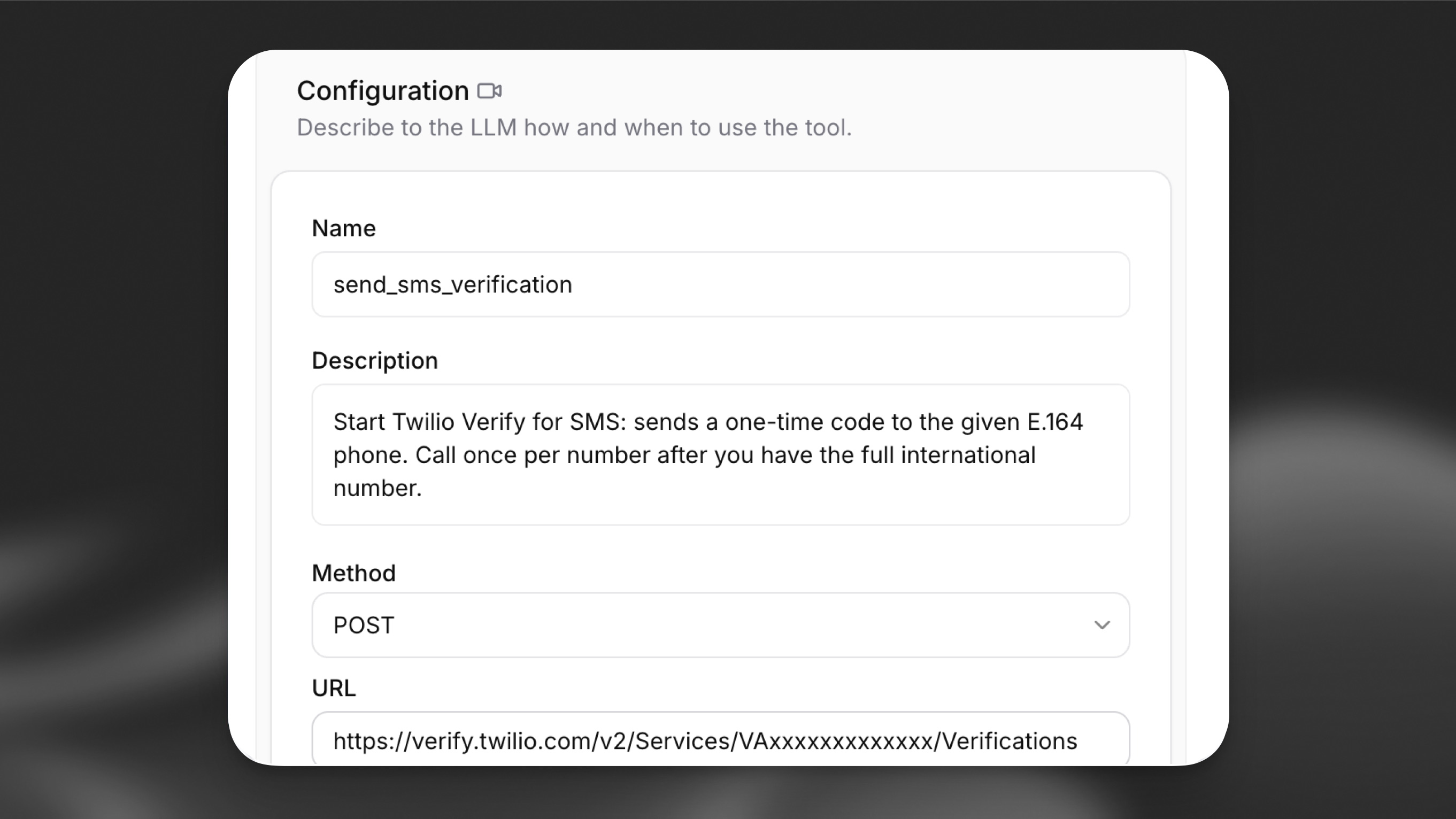
In the Agent section of your agent settings, choose Add Tool and select Webhook.
Replace YOUR_VERIFY_SERVICE_SID with the VA... SID from the first step.
Authentication header: Under Headers, add Authorization as type Secret and paste the full value (Basic plus Base64). See Server tools.
Body parameters: Set Content type to URL-encoded (application/x-www-form-urlencoded). Add parameters with LLM Prompt as the value type:
check_SMS_verification
Add a second webhook tool:
Use the same Verify Service SID and the same Authorization secret as for send_SMS_verification.
Body parameters: URL-encoded. Add To (E.164) and Code (OTP digits) with LLM Prompt.
If you configure Channel as an LLM-filled field in the dashboard, add instructions in your system prompt so the model always passes sms. The CLI and API examples above pin sms with constant_value / constantValue, so the model does not choose the channel.
Enable the skip_turn system tool
Callers often need a moment to receive the SMS before they can read the code. Without skip_turn, the agent may talk over the pause or repeat prompts.
Add via the dashboard
Add via the CLI
Add via the API
In Tools, choose Add Tool, select System tool, and enable Skip turn. No further configuration is required.
Add guidance to the system prompt so the model knows when to call it, for example:
See Skip turn for details.
Troubleshooting
Twilio 60200 — Invalid parameter (HTTP 400)
Twilio may return a body like this when the request URL or body does not match what the Verify API expects:
What to check: The path must use your Verify Service SID (VA...) from the Authenticate (Verify) service settings. Putting your Account SID (AC...) in .../Services/{Sid}/... is a frequent cause of 60200. See Twilio’s 60200 documentation for other invalid-parameter cases.
Twilio 20003 — Authentication Error — No credentials provided (HTTP 401)
When the Authorization header is missing, malformed, or not sent, Twilio can respond with:
What to check: The tool must send an Authorization header whose value is the full Basic <base64> string (including the word Basic and a single space before the Base64 output). The Base64 input must be exactly ACCOUNT_SID:AUTH_TOKEN with no extra spaces or newlines. Confirm the secret is attached to this header on both webhook tools. See 20003.
Other issues
- Number rejected in trial mode: In the Twilio Console, open Verified phone numbers and ensure the destination number is listed before you test.
- Agent talks over the caller: Confirm Skip turn is enabled and the system prompt tells the model to use
skip_turnwhen the caller needs time.