Okta SAML SSO lets workspace members sign in to ElevenLabs through an Okta SAML 2.0 app integration.
SSO is available for Enterprise workspaces. Only Workspace admins can configure SSO settings.
ElevenLabs supports Service Provider (SP) initiated SAML SSO. To start sign-in, use
https://elevenlabs.io/app/sign-in?use_sso=true. You can add email=user@example.com as a query
parameter to prefill the email field.
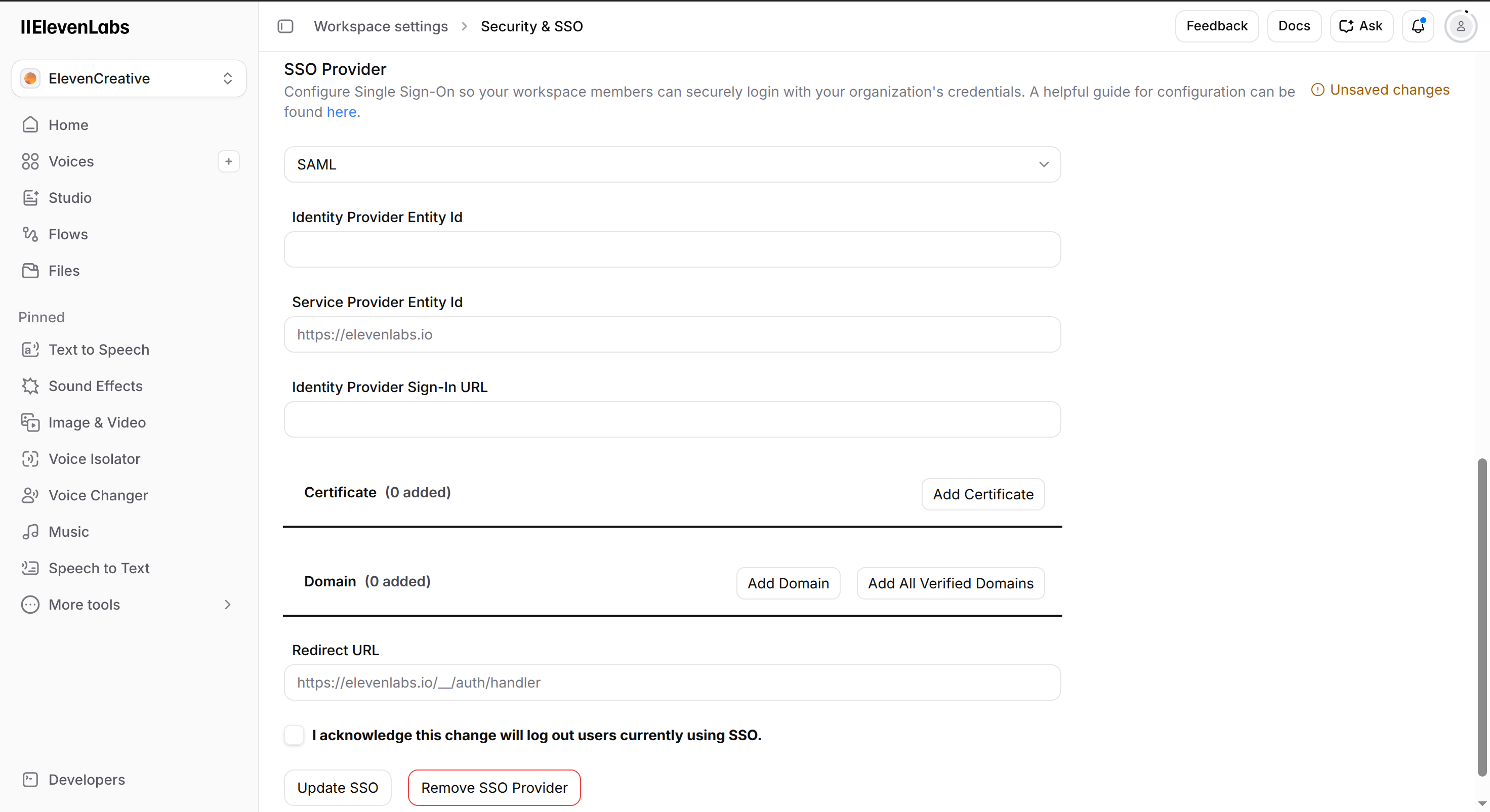
In SSO Provider, select SAML. Copy the Service Provider Entity Id and Redirect URL values. You will use these values in Okta.
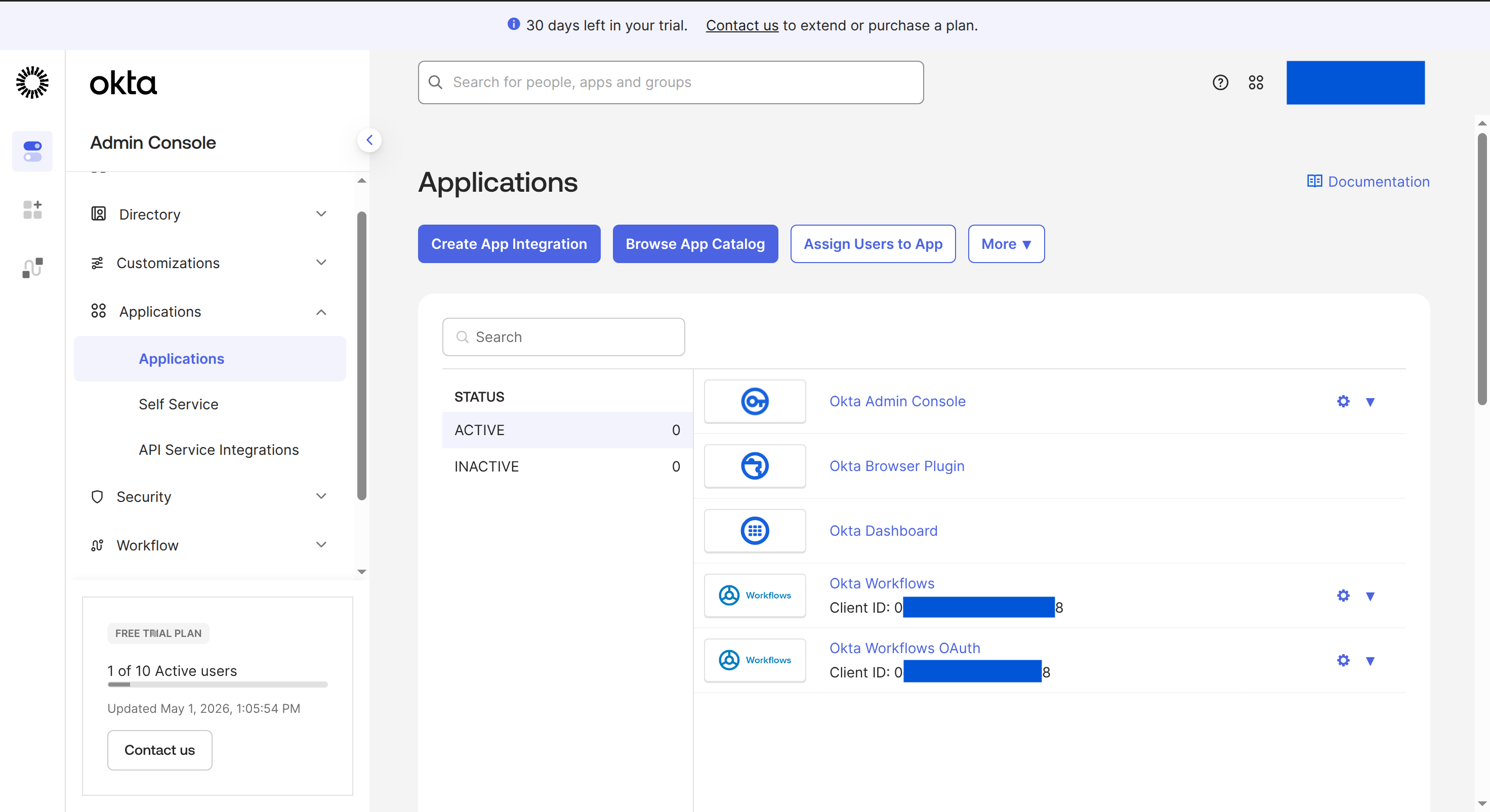
In the Okta Admin Console, go to Applications > Applications, then click Create App Integration.
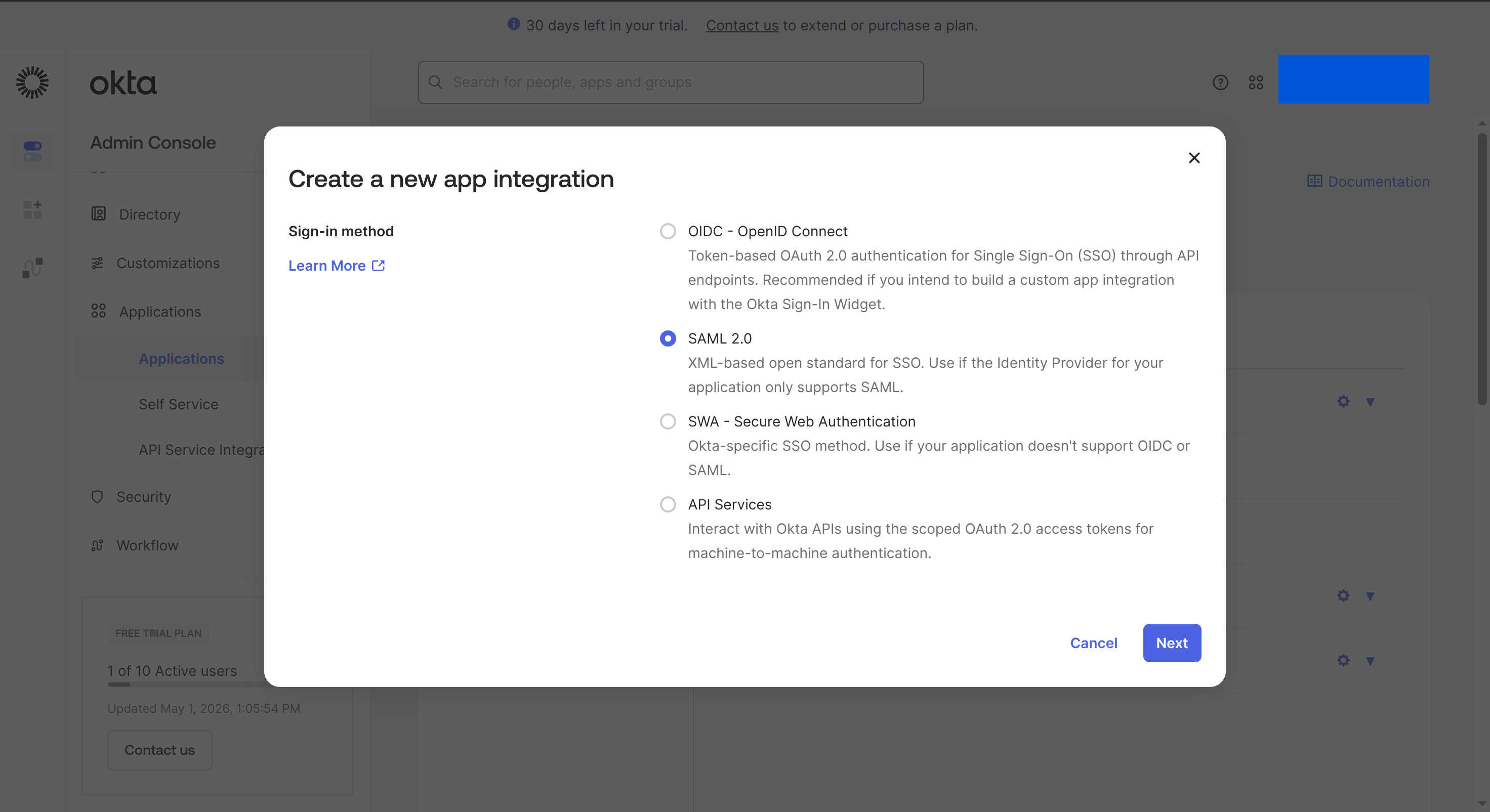
Select SAML 2.0, then click Next.
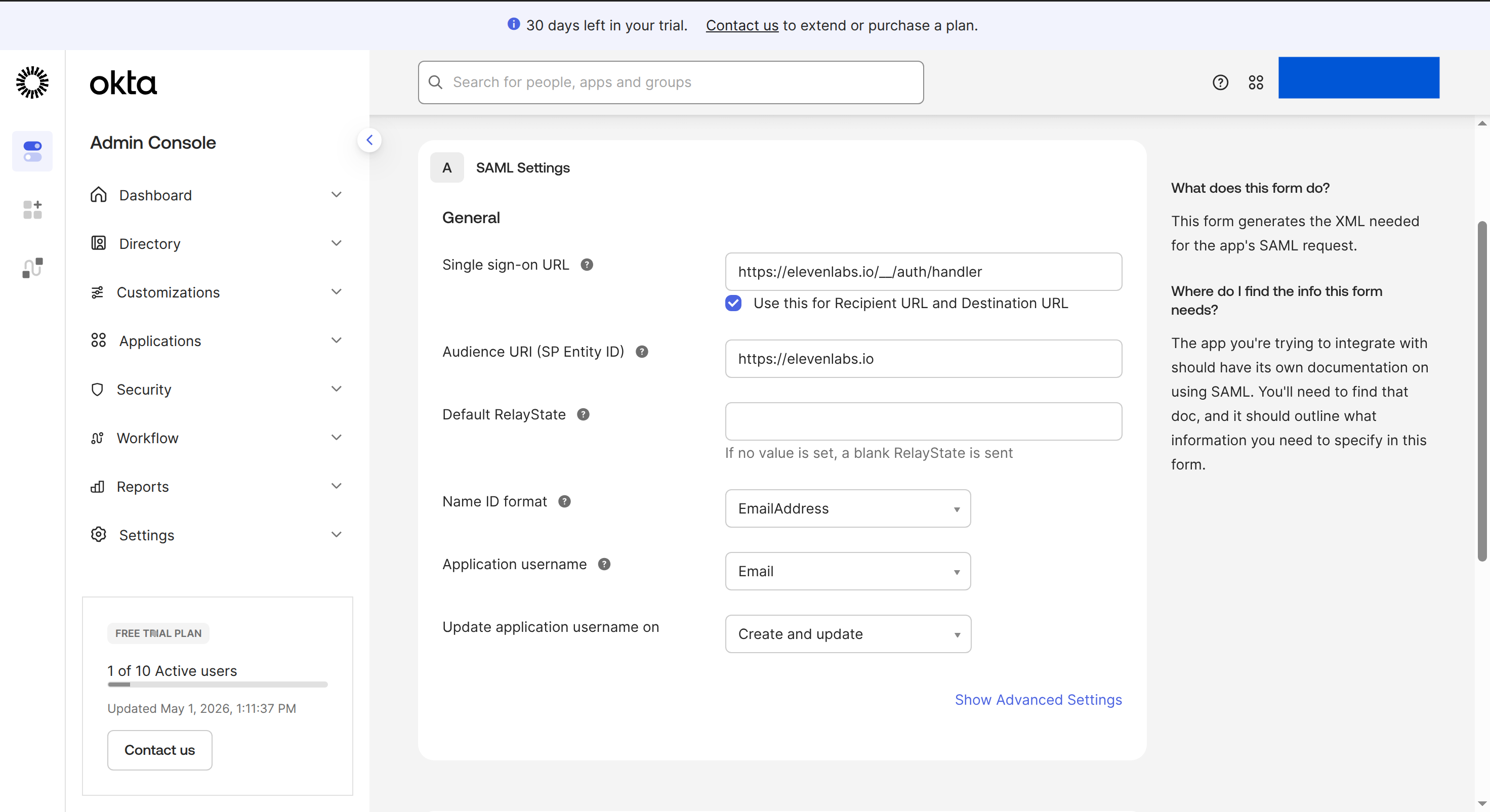
In SAML Settings, configure the app with the values from ElevenLabs:
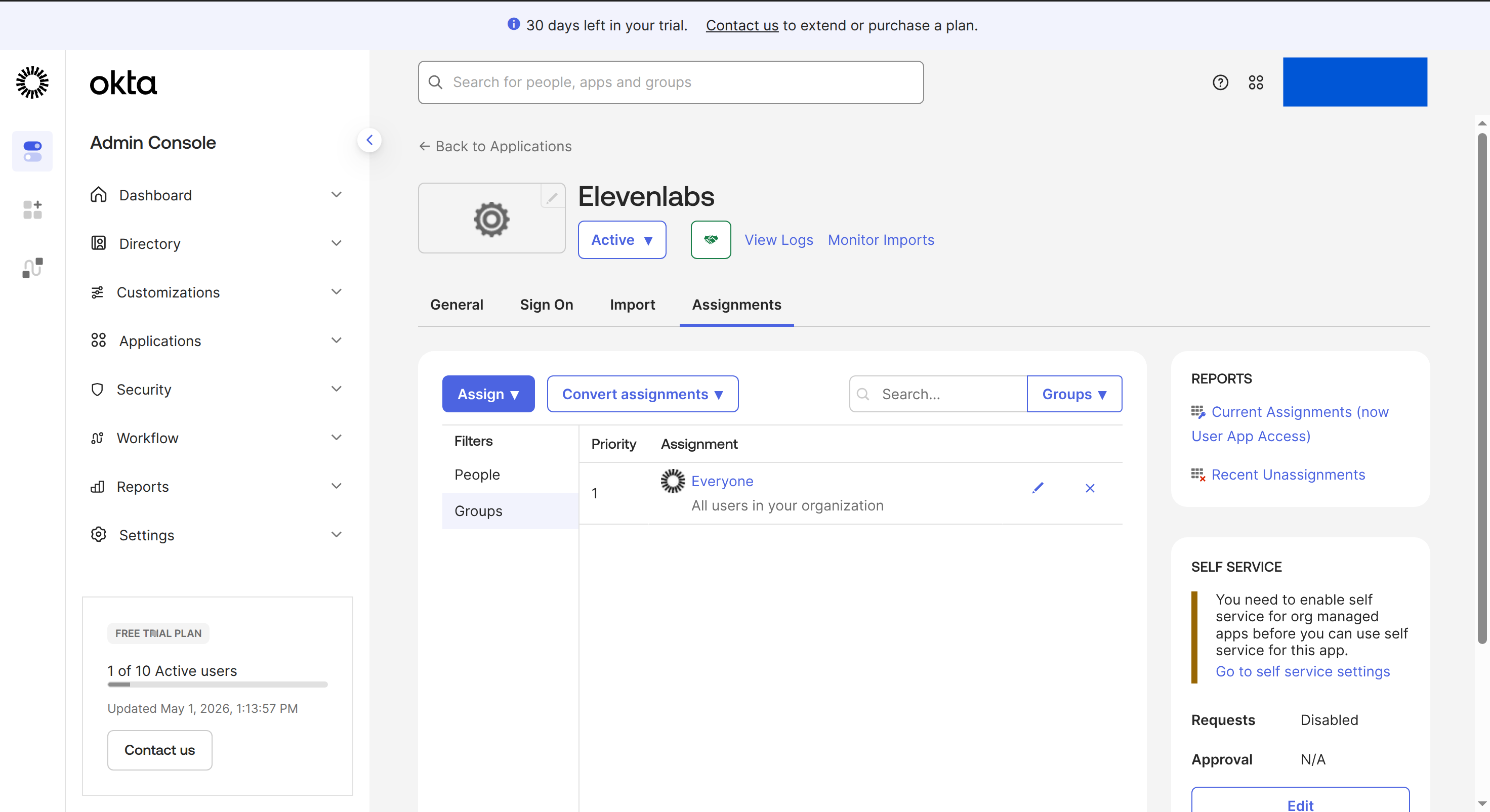
Open the Okta app’s Assignments tab and assign the users or groups that should be able to sign in to ElevenLabs.
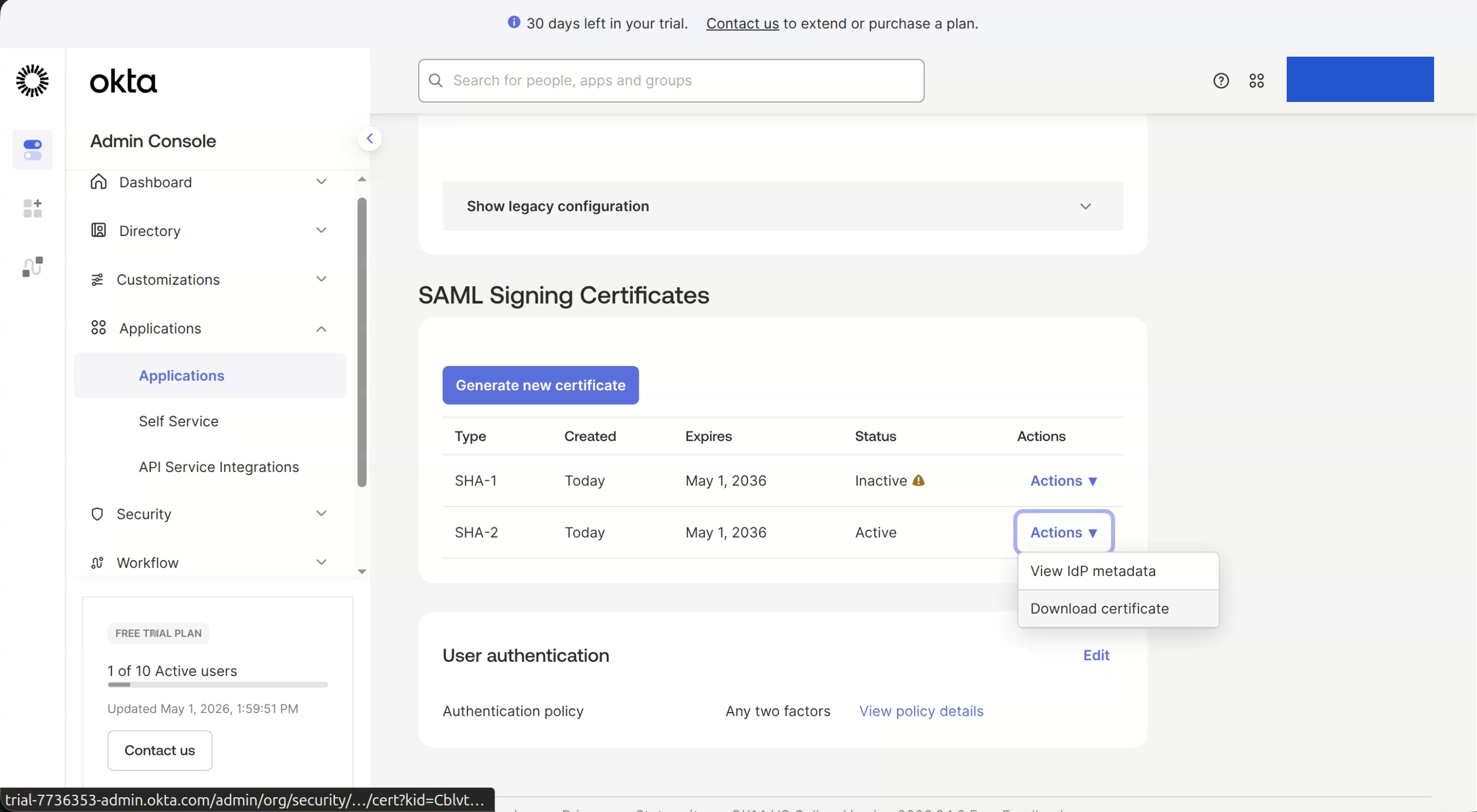
In Okta, open SAML Signing Certificates and use Actions > Download certificate for the active certificate.
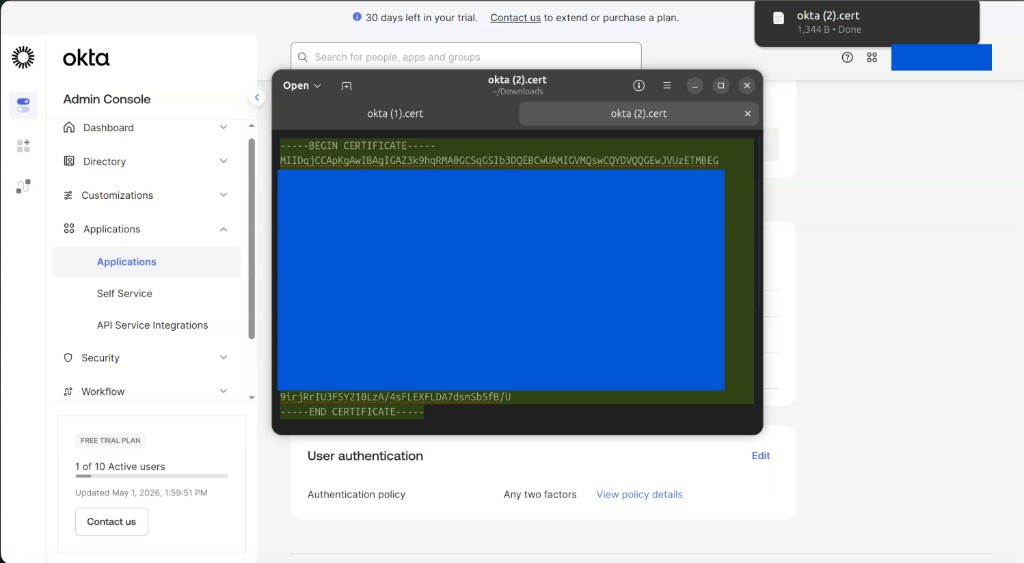
Open the certificate file and copy the full PEM certificate, including
-----BEGIN CERTIFICATE----- and -----END CERTIFICATE-----.
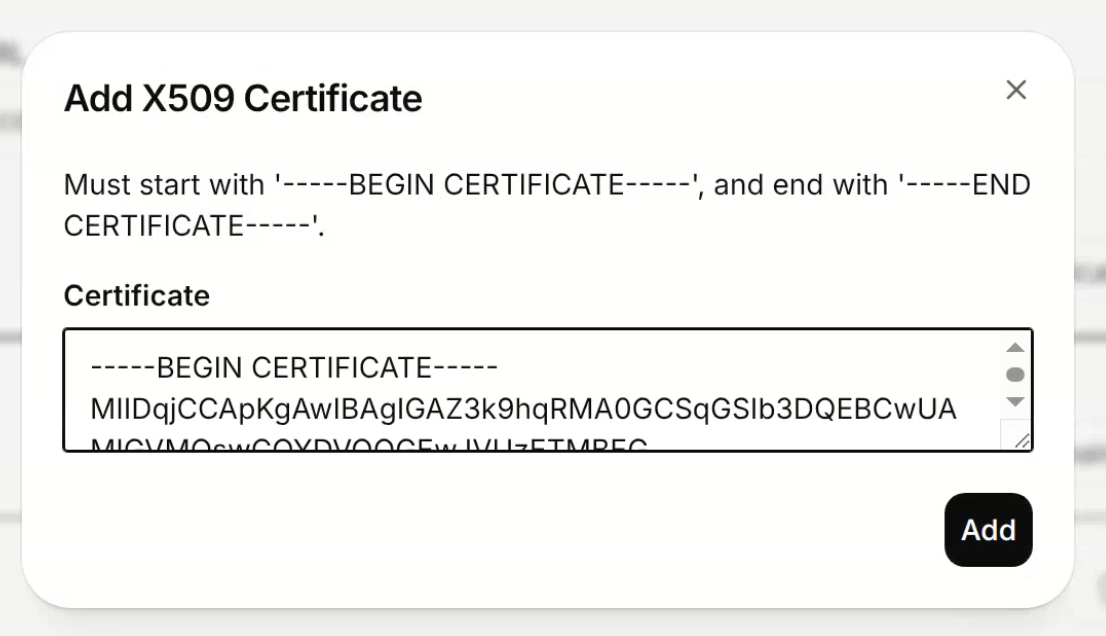
In ElevenLabs, click Add Certificate, paste the Okta certificate, then click Add.
In Okta, open the IdP metadata XML. Copy the metadata values into ElevenLabs:
entityID for Identity Provider Entity Id.SingleSignOnService Location URL that ends in /sso/saml for Identity Provider
Sign-In URL.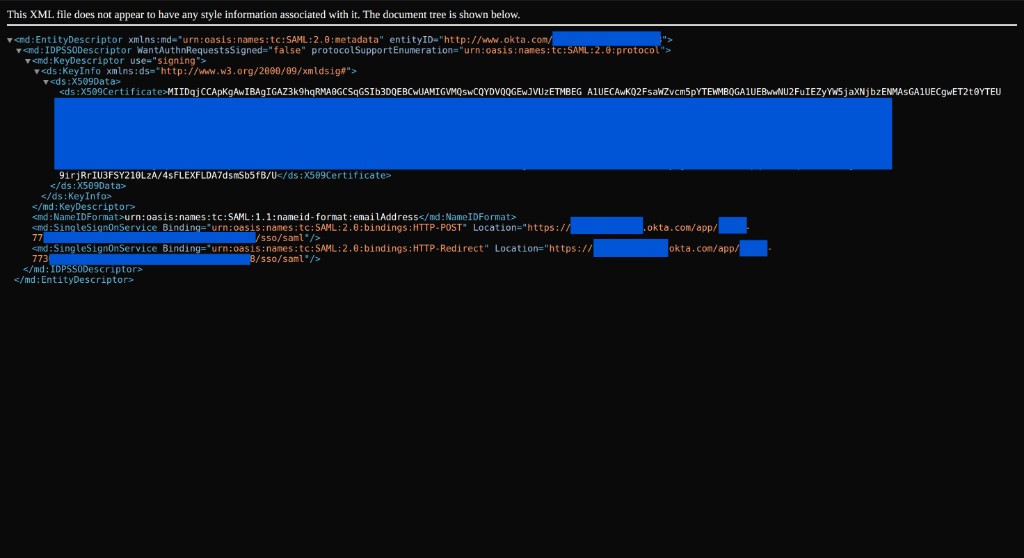
Use this table to map Okta SAML settings to ElevenLabs SSO fields.
Check the browser Network response for accounts:signInWithIdp. Okta System Log entries such as
User single sign on to app SUCCESS only confirm that Okta authenticated the user. ElevenLabs
can still reject the SAML response if the assertion values do not match the SSO configuration.
The browser Network response may show INVALID_IDP_RESPONSE: Error when parsing certificate.
Remove the certificate from ElevenLabs, then re-add the Okta X.509 certificate in valid PEM
format. Do not use an LLM to format the certificate. Copy the certificate exactly, including
-----BEGIN CERTIFICATE----- and -----END CERTIFICATE-----.
Make sure Okta sends the user’s email address as NameID. In Okta, set Name ID format to
EmailAddress and Application username to Email.
Use metadata entityID for Identity Provider Entity Id, SingleSignOnService Location for
Identity Provider Sign-In URL, and ds:X509Certificate for Certificate.